top of page


How to 10x your business intelligence with finance automation
By Geoff Charles, Head of Product, Ramp Time is the only asset a business can never fully recoup. For companies looking to become leaders...
6 min read

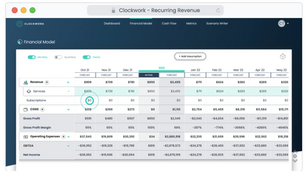
How to Easily Forecast Recurring Revenue Using Clockwork
Clockwork made a solution for forecasting and modeling recurring revenue. Startup founders will want to see how easy it is!
2 min read


How to Build a Marketing Technology Stack (MarTech Stack) for Your Startup
Creating a robust marketing technology stack helps to increase your teams’ efficiency and improve all corners of your marketing...
6 min read


How to Create an Effective Drip Campaign in Mailchimp
Learn how to craft compelling Mailchimp drip campaigns that convert leads into loyal customers. Follow these 5 email nurture best practices.
6 min read

How Chatbots Work as Digital Marketing Funnel Automation Tools
No longer a novelty, chatbots are becoming an increasingly popular digital marketing funnel automation tool, providing businesses a way...
6 min read


Capital-as-a-Service: A Funding Model to Help Startups Grow
What is Capital-as-a-Service and how does it work? We explain this beneficial funding solution for growing Saas startups.
3 min read


Cloud Storage Comparison: 5 Best Options for Startups
Your startup has lots of files to store and to share with your team, your investors, and your customers. The most practical way to store...
4 min read


Business Intelligence Software: 5 Best Options for Small Business
While B2B SaaS companies know the value of data better than most, they haven’t always implemented effective ways to capture the data that...
2 min read


Why Your Startup Should Use Two-Factor Authentication (And How to Enable it)
For just about any kind of business, one of your most valuable assets is your data. Whether you manufacture physical goods or sell...
4 min read


7 Best Small Business Accounting Software Options
Accounting software is far more powerful than Excel and should easily streamline all of your startup's finances. Here are 7 good solutions.
5 min read

Introducing Client Perks: Discounted Business Tools for Scaling Your Startup
We love our clients; after all, we succeed only when our clients succeed. As part of our mission to help you scale your startup, we want...
3 min read
bottom of page